The headlines on ransomware attacks keep coming, and they’re scary.
Now, the White House is asking corporations and small business owners to fight back by taking steps to increase security and prevent the next Colonial Pipeline cyberattack from happening.
“The threats are serious, and they are increasing,” Anna Neuberger, cybersecurity adviser at the National Security Council wrote in a memo to corporate executives and business leaders. “We urge you to take these critical steps to protect your organizations and the American public.”
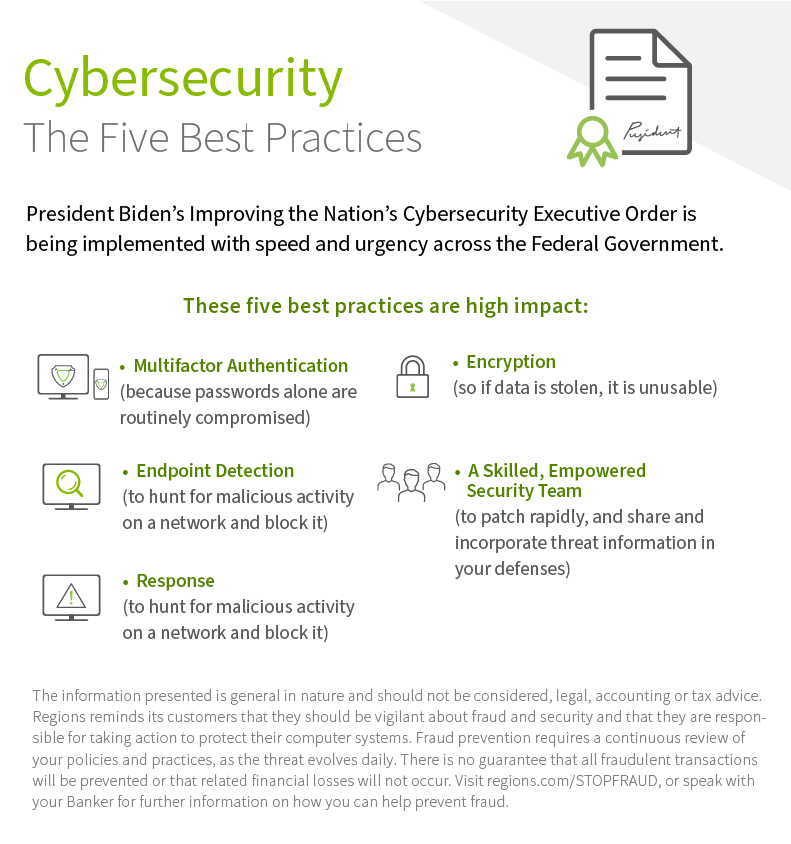
President Biden signed an executive order in May. Called Improving the Nation’s Cybersecurity, the order outlines five best practices that have the highest impact in preventing attacks.
“It’s not just the attacks on critical infrastructure that have prompted the attention of the Federal government,” said Jeff Taylor, head of commercial fraud forensics for Regions Bank. “Ransomware continues to be a pervasive threat to businesses of all sizes and segments. These guidelines will assist in your preparation, protection, and event response.”
In her memo, Neuberger recommends both public and private entities work together on these steps:
- Implement the five best practices from the President’s Executive Order: These five best practices are high impact — multifactor authentication (because passwords alone are routinely compromised), endpoint detection and response (to hunt for malicious activity on a network and block it), encryption (so if data is stolen, it is unusable) and a skilled, empowered security team (to patch rapidly, and share and incorporate threat information in your defenses).
- Backup your data, system images, and configurations, regularly test them, and keep the backups offline: Ensure that backups are regularly tested and that they are not connected to the business network, as many ransomware variants try to find and encrypt or delete accessible backups. Maintaining current backups offline is critical because if your network data is encrypted with ransomware, your organization can restore systems.
- Update and patch systems promptly: This includes maintaining the security of operating systems, applications, and firmware, in a timely manner. Consider using a centralized patch management system; use a risk-based assessment strategy to drive your patch management program.
- Test your incident response plan: There’s nothing that shows the gaps in plans more than testing them. Run through some core questions and use those to build an incident response plan: Are you able to sustain business operations without access to certain systems? For how long? Would you turn off your manufacturing operations if business systems such as billing were offline?
- Check Your Security Team’s Work: Use a 3rd party pen tester to test the security of your systems and your ability to defend against a sophisticated attack. Many ransomware criminals are aggressive and sophisticated and will find the equivalent of unlocked doors.
- Segment Your Networks: There’s been a recent shift in ransomware attacks – from stealing data to disrupting operations. It’s critically important that your corporate business functions and manufacturing/production operations are separated and that you carefully filter and limit internet access to operational networks, identify links between these networks and develop workarounds or manual controls to ensure ICS networks can be isolated and continue operating if your corporate network is compromised. Regularly test contingency plans such as manual controls so that safety critical functions can be maintained during a cyber incident.
All organizations must recognize that no company is safe from being targeted by ransomware attacks, regardless of size or location. But there are immediate steps you can take to protect yourself, as well as your customers and the broader economy.
Anna Neuberger, cybersecurity adviser at the National Security Council
Neuberger said that the number of cyberattacks have increased significantly, and strengthening resilience is a priority of the administration.
“The private sector also has a critical responsibility to protect against these threats,” she added. “All organizations must recognize that no company is safe from being targeted by ransomware attacks, regardless of size or location. But there are immediate steps you can take to protect yourself, as well as your customers and the broader economy.”
For more information on ransomware:
The information presented is general in nature and should not be considered, legal, accounting or tax advice. Regions reminds its customers that they should be vigilant about fraud and security and that they are responsible for taking action to protect their computer systems. Fraud prevention requires a continuous review of your policies and practices, as the threat evolves daily. There is no guarantee that all fraudulent transactions will be prevented or that related financial losses will not occur. Visit regions.com/STOPFRAUD or speak with your Banker for further information on how you can help prevent fraud.