It’s a tool you use every day. And it’s capable of creating complete financial chaos for your company.
“Laptops are value-rich with information,” said Randy Wilborn, a senior product manager with Regions’ Treasury Management team. “We often see dates of birth, Social Security numbers, vendor data and credit card information stored on them, as well as on jump drives easily accessible to others.”
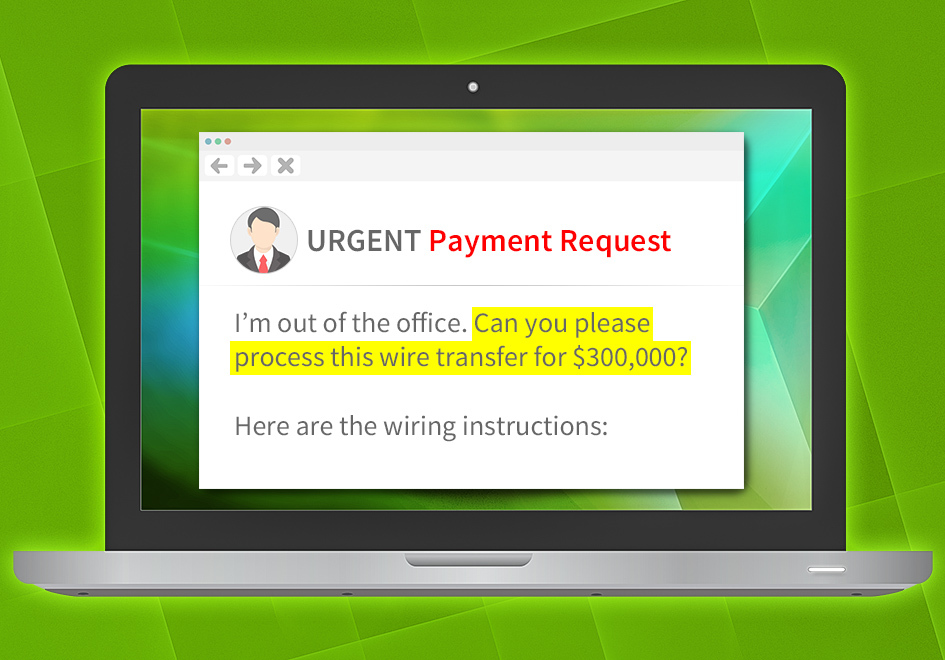 Look out for emails that appear to be from a manager or a colleague, urgently asking for a large sum of money to be transferred. It pays to verify the authenticity of the message before initiating the transaction.
Look out for emails that appear to be from a manager or a colleague, urgently asking for a large sum of money to be transferred. It pays to verify the authenticity of the message before initiating the transaction.
Wilborn’s remarks were part of a recent Fraud Prevention and Awareness seminar held for Regions’ Commercial Banking clients in Indianapolis.
Darah Watson is one of them.
“Fraud is something that can potentially affect every aspect of our business,” said Watson, president of Sandlian Management Corporation. Sandlian operates U-STOR Self Storage locations in four states.
Beyond attending the program, Watson regularly reads fraud articles to remain current on trends. “With everything going on, I really try to keep up,” she said. “If I stop learning, I become an ineffective manager.”
 Leaders from Regions Bank and the Indianapolis Metropolitan Police Department held two recent fraud-prevention seminars as part of ongoing efforts to help people and businesses spot fraud and protect their accounts.
Leaders from Regions Bank and the Indianapolis Metropolitan Police Department held two recent fraud-prevention seminars as part of ongoing efforts to help people and businesses spot fraud and protect their accounts.
Keeping up with fraud fills Matt Reidenbach’s days. Reidenbach, a lead detective for the Indianapolis Metropolitan Police Department’s Organized Crime Unit, also served as a seminar panelist. Reidenbach noted scammers are not only becoming more adept in their methods, but also expanding their reach with technology. So police departments are working together to catch crooks who reach across city and state lines.
“You can chase these all day,” Reidenbach noted. “We easily see 100 fraud cases that occur over a weekend. I can’t overstate the importance of putting safeguards in place.”
So, what can business owners do to combat potential fraud? Here are four easy tips you can start implementing today:
1. Be Forward Thinking with Financial Transaction Emails:
“I recommend using the forward key rather than just hitting reply to messages involving financial transactions,” said Neil Taylor, Regions’ Area Security Manager for Indiana. Given the rise of business email compromise, an email that looks like it’s from a company official asking you to move some money … might actually be from someone else. “Someone may try to make you think it’s them with an email address so slightly different that you don’t realize it’s not legitimate. But if, instead of replying to that sender, you forward the message and type in the address of the company official manually, you can confirm it’s the person you’re intending to connect with.”
2. Remember, It Takes Two:
Enlist a two-factor authorization process on any emails related to payment authorization changes. By establishing and adhering to an internal checks-and-balances approach requiring a second person to verify any account changes, you can have greater peace of mind.
3. Be Password Proactive and Protective:
You might think it goes without saying that your password shouldn’t be “password.” But that ranks at the top of the list for many people as their not-so-secret word to access their accounts. Others include 123456, 123456789 and qwerty, made up of the top row of keys on the left side of the keyboard. “Passwords should be changed every 60 days,” said Wilborn. “And they should be at least 8 characters and include a number and a symbol so that it’s not an easy task for scammers to access your accounts.”
4. Take Your Time:
Slowing down to give your security the time and attention it deserves can thwart a potential cyber threat. “Everybody’s busy these days,” said Taylor. “But it often takes less than five minutes to make that phone call and verify a transaction rather than exclusively communicating by email. It’s five minutes that can mean the difference of giving someone free reign to your email inbox and your life.”
Watson plans to share information from the session with her Sandlian colleagues.
“We do employee training on security best practices,” said Watson. “It’s about keeping the information of our customers safe. I’m vigilant about it.”